Here is a hodge-podge of links that stood out this week.
Tr3Secure Data Collection Script Reloaded - Journey Into Incident Response blog - Corey Harrell has new news and updated on the Tr3Secure Volatile Data Collection Script he developed some time ago.
Tr3Secure Data Collection Script Reloaded - Journey Into Incident Response blog - Corey then follows up with a “real-world” walkthough of the Tr3Secure Volatile Data Collection Script after purposefully a lab pc for the sake of the discussion. It’s one thing to read about what a tool and process can do, it is a real treat to have the author lead a guided walkthough of the tool in action. As always, don’t forget to follow up with a comments reading as well.
plaso - super timeline - from the website “Plaso (plaso langar að safna öllu) is the Python based back-end engine used by tools such as log2timeline for automatic creation of a super timelines. The goal of log2timeline (and thus plaso) is to provide a single tool that can parse various log files and forensic artifacts from computers and related systems, such as network equipment to produce a single correlated timeline. This timeline can then be easily analysed by forensic investigators/analysts, speeding up investigations by correlating the vast amount of information found on an average computer system.” Spotted via this CDF at Champlain post.
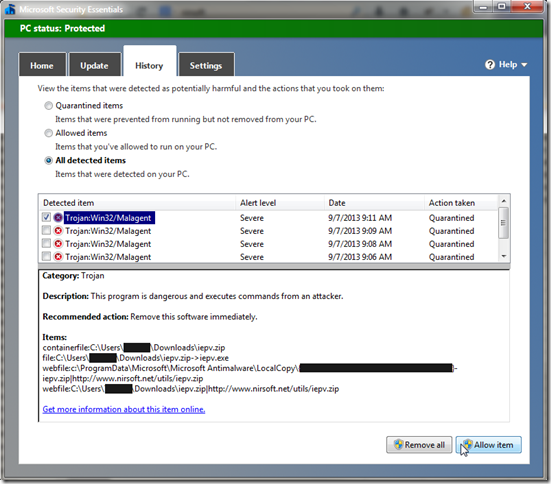
Microsoft Security Essentials: Aiming low? - ZDNet - Larry Seltzer offers some thoughts on Microsoft’s free AV solution. He really doesn’t thrash MSE but does point out that there are many other free alternatives that tend to perform higher. It seems like a pretty reasonable perspective. FYI, I have been debating making a change from Microsoft Security Essentials to Bitdefender Antivirus Free. Yesterday I uninstalled MSE and replaced it with BAF. The changeover went very smooth. The deciding factor for me was the ongoing poor post-boot performance of my system. While I don’t have a SSD drive in my laptop, I is running an Intel i7 CPU with 8 GB RAM. After boot, MSE scans on the post boot environment seem to be leading to slower post-boot launch of a number of my applications for a while as processes and files get scanned. Now that I am on BAF, I don’t see those post-boot application hangs. That said, I will continue to primarily recommend MSE to family and friends unless repeated infections indicate a need for the advance protection BAF may provide.
Before moving on from Microsoft Secuirty Essentials and Windows Defender (for Win 8), I thought this post Windows Defender and context menu for file check? (GTranslated) at Borns IT and Windows Blog was very insightful. Some time ago I posted a number of Windows Defender tweaking tips Advanced Tips for Windows Defender with Windows 8, one of which was how to add a scan with Windows Defender to the context menu list in Win 8. Born’s acknowledges that is a popular request and go though how it is accomplished. However, as he points out, the way Windows Defender operates, when a file is accessed via the (File) Explorer, Windows Defender already scans it before allowing access. If it is infected then you don’t get to fiddle with it. Same thing with downloaded files; again pre-scanned by Windows Defender. So, you can manually scan them again if you want, but know that if you do use Windows Defender in Win 8, it has already scanned the file.
Message Analyzer has Released – A New Beginning and Message Analyzer: Why so different from Network Monitor? - MessageAnalyzer Blog - Final release now public for Microsoft’s network capture analysis tool. I’m not sure it will replace Wireshark, but the approach is a step up from their older Network Monitor capture tool and is at the very minimum a great supplemental network capture tool for packet analysis.
Plugin Activation in Firefox - Mozilla Add-ons Blog - basically in a future version of Firefox, all plugins (except Flash) will become “click-to-activate”. This may or may not be a great thing depending on your security versus convenience perspective.
Wendel's Small Hacking Tricks - Killing Processes from the Microsoft Windows Command Line interface - SpiderLabs Anterior - I’m always looking to find a way to do something without a third-party tool so this is handy information to be familiar with.
Universal USB Installer (also YUMI) USB Flash drive does not boot on EeePC - RMPrepUSB, Easy2Boot and USB booting... blog - This is a pretty esoteric technical post for most folks, however if you are into USB-based system booting, it is interesting.
When setting up Windows 8.1, Microsoft appears to do all it can to shove you to create/use an on-line Microsoft account rather than a local one. For some folks that might be fine but others (particularly the old-school crowd) will find this process similar to a cattle chute. If you are a thinking cow, it probably isn’t a very pleasant experience. Fortunately, there seem to be a number of outs if you know the game ahead of time.
- How To Install Windows 8.1 Without Microsoft Account - Into Windows
- Use Windows 8.1 with a local account instead of a Microsoft account - 4sysops
- How to setup local account in Windows 8.1 - DeDoimedo.com
- Windows 8.1 How To Convert Windows Live Account To Local Account - Next of Windows
Group Policy Search Engine Gets Updated - Group Policy Central blog - From that post by Alan Burchill:
“The Group Policy Search Engine is a great web site that has all the different version of Microsoft Group Policy ADMX files that allows you to easily and quickly search for the policy setting. This site is one I use very frequently especially and is a must have bookmark for any Group Policy Administrator.
“Well, Stephanus from Microsoft who maintains the web site has just loaded the Windows 8.1 and Windows Server 2012 R2 policy setting meaning you can now look up all the new policy setting in the latest version of Windows. “
Group Policy Search - site homepage.
Google Static Map Maker: Static Maps on Steroids - noupe - Nice tool to create linkable custom static Google maps rather than using a screen-shot image or a embedded and modifiable one.
Google Static Map Maker - site homepage by Katy Decorah.
Cheers!
--Claus Valca